AI Readiness
Needs Improvement
Cyflow AI Readiness helps MSPs, IT, and security teams quickly see what Copilot and Gemini can access across Microsoft 365 and Google Workspace, uncover Shadow AI and SaaS app exposure, and prioritize the highest-risk remediation steps before rollout.
See what Copilot can access in your tenant — and what to fix before rollout.
Read-only access · 30-second setup · No credit card
By submitting, you agree to our Terms and Privacy Policy.

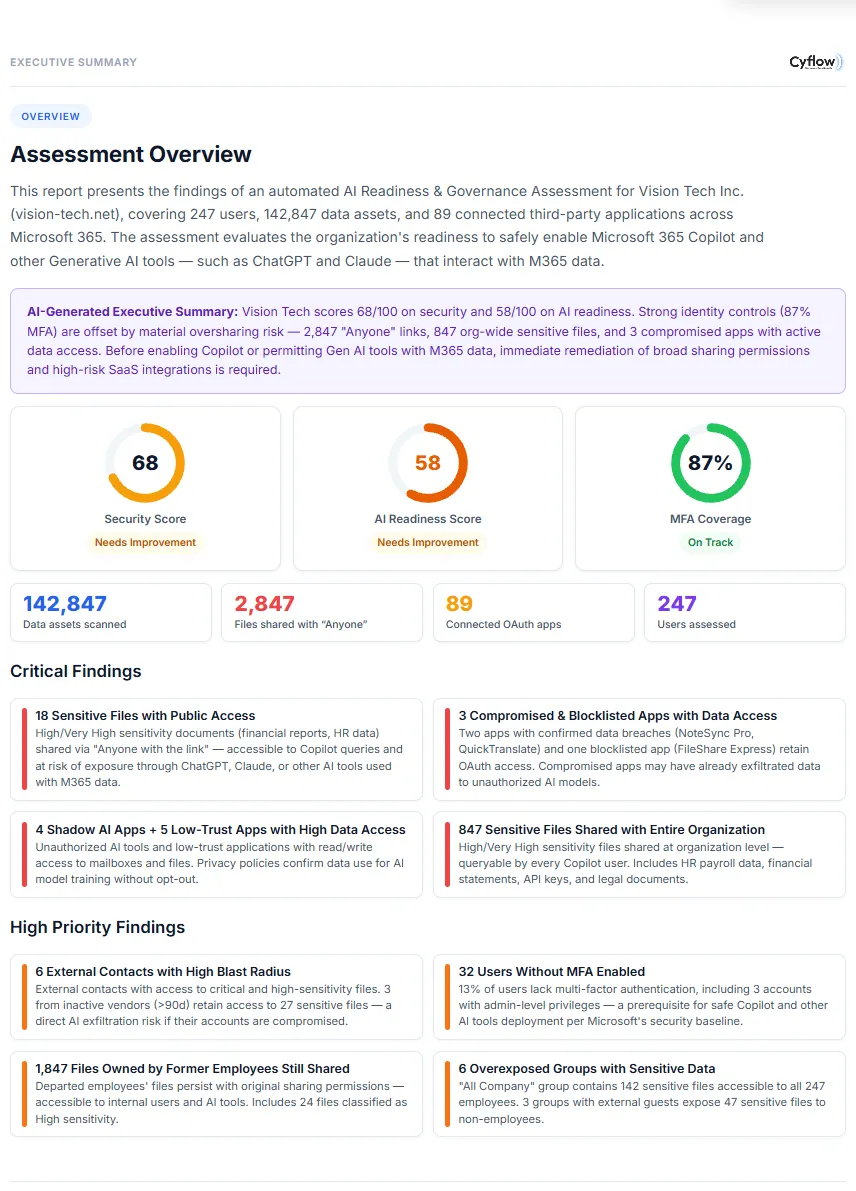
Sample scores from a 247-user enterprise tenant.
Needs Improvement
Needs Improvement
Needs Improvement
On Track
Surface public links, broad sharing patterns, and sensitive file access paths that increase AI-era risk.
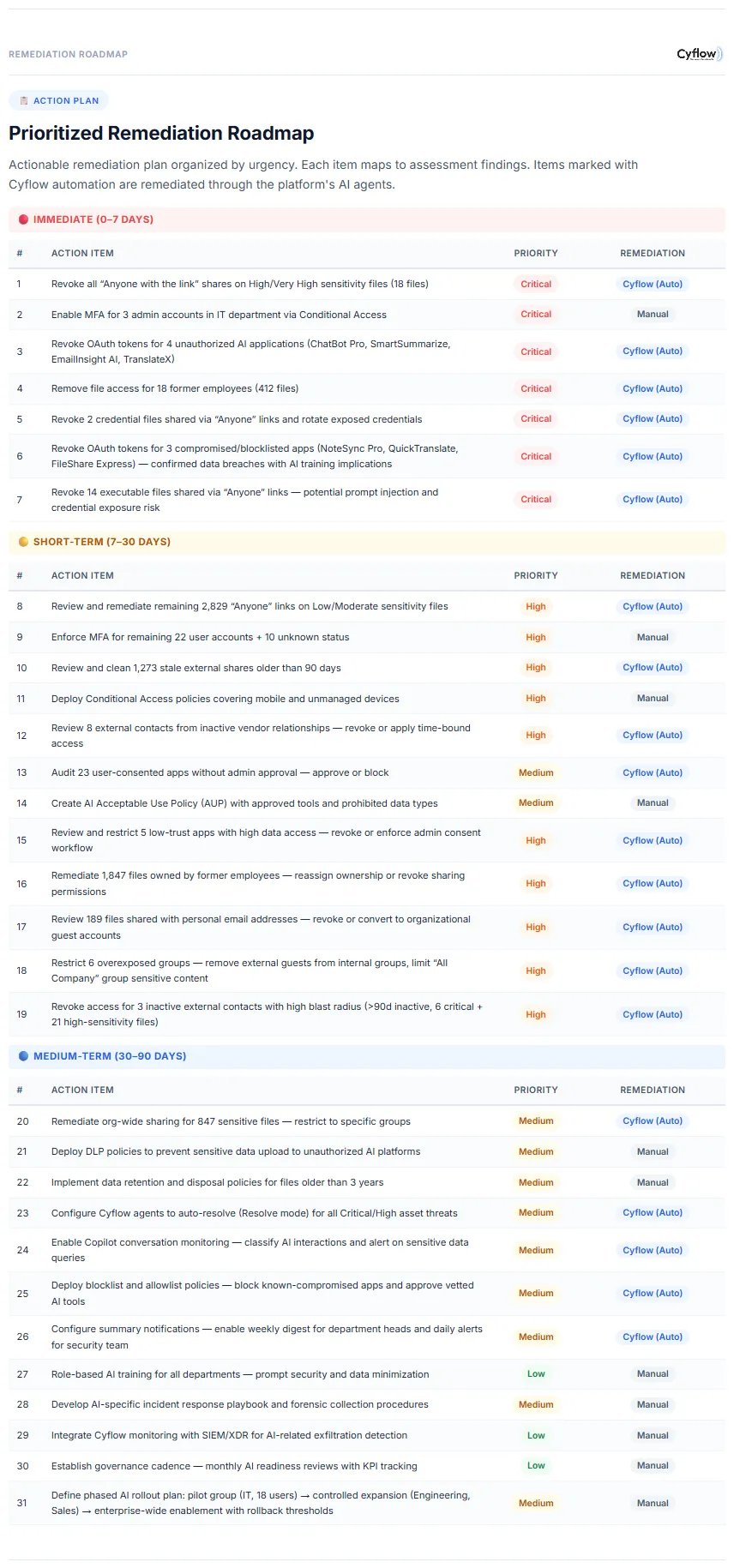
Start with clear actions your team can execute quickly, then track posture improvements over time.
Give security leaders and IT owners one place to evaluate risk posture before broader AI enablement.
Executive summary, score breakdowns, and prioritized remediation guidance for stakeholders.
Find risky sharing posture, compromised app patterns, and high-priority user access issues.
Get practical next steps with clear ownership and quick-win sequencing for your security team.
Use concrete examples to align IT and security leaders before wider AI enablement.
Critical
18 sensitive files with public access
Critical
3 compromised and blocklisted apps with active data access
High
4 shadow AI apps and 5 low-trust apps discovered
High
847 sensitive files shared org-wide
High
32 users without MFA enabled
Medium
16 external contacts with high blast radius across shared drives
“The AI readiness report surfaced critical oversharing issues we had no visibility into. After remediating them, we deployed Copilot with confidence.”
IT Director, Mid-Market Technology Company
Purview is powerful but often configuration-heavy. Cyflow is built for rapid onboarding and actionable remediation in one flow.
Onboarding takes around 30 seconds, and a full assessment is typically ready within a few hours for a mid-sized tenant.
Cyflow uses read-only scopes where possible, encrypted transport/storage, and does not use tenant data for model training.
It evaluates your current sharing, identity, and app-risk posture so you can reduce AI-era data exposure before broad Copilot rollout.
Onboarding typically takes about 30 seconds, and first signals usually appear within minutes as initial scans complete.
No. Cyflow operates for security posture analysis and remediation workflows, not model training.
Cyflow reporting and controls align with common enterprise practices including NIST AI RMF, OWASP LLM Top 10, ISO 27701, and SOC 2 expectations.
Yes. Cyflow supports Microsoft 365 and Google Workspace environments, including Gemini-related exposure considerations.
Purview is powerful but often configuration-heavy. Cyflow focuses on rapid onboarding, exposure visibility, and remediation workflows in one flow.